X User sent me the following that this stopped working in May, 2024: https://x.com/M0teki/status/1821953030293524860
Direct Link: https://github.com/0xDanielLopez/TweetFeed
☰ Content
❤️ Support the project
If you like the project, please consider:
- Giving it a star ⭐
- Invite to a coffee ☕
📄 Data collected
Feeds
| 2024-08-09 14:10:18 (UTC) | |||
|---|---|---|---|
| Today | Last 7 days | Last 30 days | Last 365 days |
| 📋 Today (raw) | 📋 Week (raw) | 📋 Month (raw) | 📋 Year (raw) |
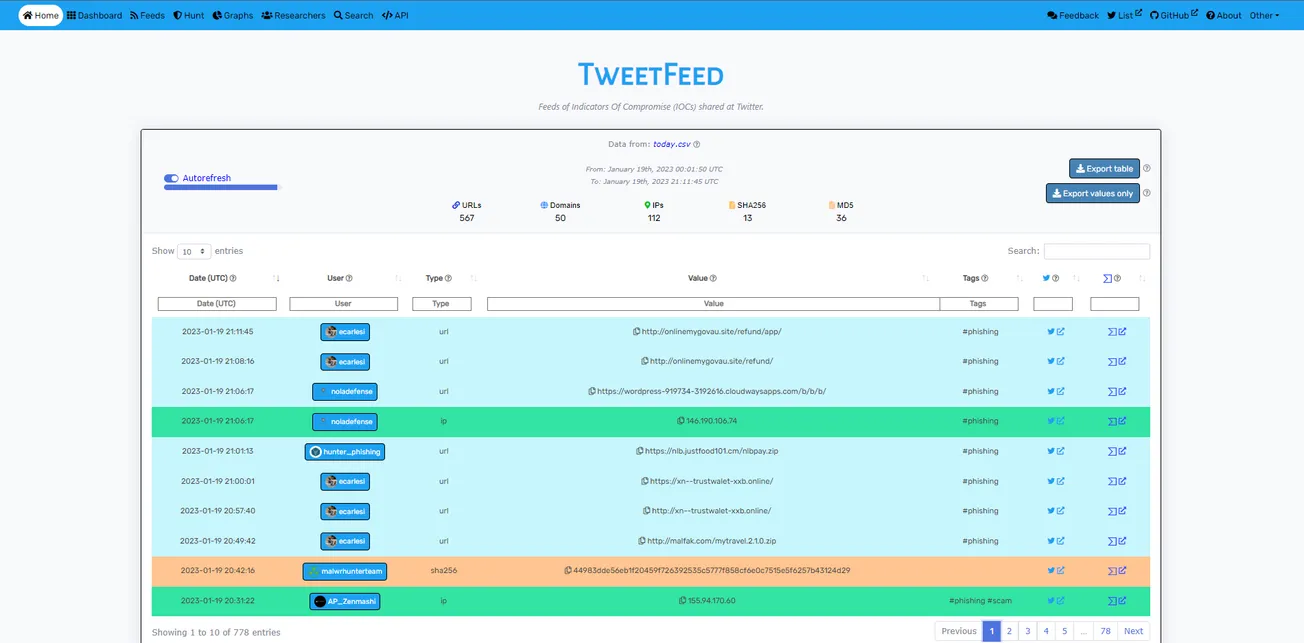
Output example
| Date (UTC) | SourceUser | Type | Value | Tags | Tweet |
|---|---|---|---|---|---|
| 2021-08-14 02:26:32 | phishunt_io | url | https://netflix.us2.cards/ | #phishing #scam | https://twitter.com/phishunt_io/status/1426369619422502917 |
| 2021-08-17 12:15:00 | TheDFIRReport | ip | 185.56.76.94 | #Trickbot | https://twitter.com/TheDFIRReport/status/1427604874053578756 |
📊 Some statistics
Types
| Type | Today | Week | Month | Year |
|---|---|---|---|---|
| 🔗 URLs | 0 | 0 | 0 | 27641 |
| 🌐 Domains | 0 | 0 | 0 | 17754 |
| 🚩 IPs | 0 | 0 | 0 | 11472 |
| 🔢 SHA256 | 0 | 0 | 0 | 4260 |
| 🔢 MD5 | 0 | 0 | 0 | 948 |
Tags
| Tag | Today | Week | Month | Year |
|---|---|---|---|---|
| #phishing | 0 | 0 | 0 | 34128 |
| #scam | 0 | 0 | 0 | 802 |
| #opendir | 0 | 0 | 0 | 335 |
| #malware | 0 | 0 | 0 | 2521 |
| #maldoc | 0 | 0 | 0 | 6 |
| #ransomware | 0 | 0 | 0 | 154 |
| #banker | 0 | 0 | 0 | 10 |
| #AgentTesla | 0 | 0 | 0 | 60 |
| #Alienbot | 0 | 0 | 0 | 0 |
| #AsyncRAT | 0 | 0 | 0 | 98 |
| #Batloader | 0 | 0 | 0 | 0 |
| #BazarLoader | 0 | 0 | 0 | 3 |
| #CobaltStrike | 0 | 0 | 0 | 6255 |
| #Dcrat | 0 | 0 | 0 | 483 |
| #Emotet | 0 | 0 | 0 | 0 |
| #Formbook | 0 | 0 | 0 | 7 |
| #GootLoader | 0 | 0 | 0 | 115 |
| #GuLoader | 0 | 0 | 0 | 21 |
| #IcedID | 0 | 0 | 0 | 8 |
| #Lazarus | 0 | 0 | 0 | 27 |
| #Lokibot | 0 | 0 | 0 | 241 |
| #log4j | 0 | 0 | 0 | 0 |
| #Log4shell | 0 | 0 | 0 | 0 |
| #Njrat | 0 | 0 | 0 | 1396 |
| #Qakbot | 0 | 0 | 0 | 1107 |
| #Raccoon | 0 | 0 | 0 | 0 |
| #RedLine | 0 | 0 | 0 | 229 |
| #Remcos | 0 | 0 | 0 | 232 |
| #RaspberryRobin | 0 | 0 | 0 | 18 |
| #Spring4Shell | 0 | 0 | 0 | 0 |
| #SocGolish | 0 | 0 | 0 | 7 |
| #Ursnif | 0 | 0 | 0 | 0 |
Top Reporters (today)
| Number | User | IOCs |
|---|---|---|
| #1 | - | 0 |
| #2 | - | 0 |
| #3 | - | 0 |
| #4 | - | 0 |
| #5 | - | 0 |
| #6 | - | 0 |
| #7 | - | 0 |
| #8 | - | 0 |
| #9 | - | 0 |
| #10 | - | 0 |
❓ How it works?
Search tweets that contain certain tags or that are posted by certain infosec people.
Tags being searched
(not case sensitive)
- #phishing
- #scam
- #opendir
- #malware
- #maldoc
- #ransomware
- #banker
- #AgentTesla
- #Alienbot
- #AsyncRAT
- #BazarLoader
- #Batloader
- #CobaltStrike
- #Dcrat
- #Emotet
- #Formbook
- #GootLoader
- #GuLoader
- #IcedID
- #Lazarus
- #Lokibot
- #log4j
- #Log4shell
- #Njrat
- #Qakbot
- #Raccoon
- #RedLine
- #Remcos
- #RaspberryRobin
- #Spring4Shell
- #SocGholish
- #Ursnif
Also search Tweets posted by
(these are trusted folks that sometimes don't use tags)
🔍 Hunting IOCs via Microsoft Defender
1. Search SHA256 hashes with yearly tweets feed
let MaxAge = ago(30d);
let SHA256_whitelist = pack_array(
'XXX' // Some SHA256 hash you want to whitelist.
);
let TweetFeed = materialize (
(externaldata(report:string)
[@"https://raw.githubusercontent.com/0xDanielLopez/TweetFeed/master/year.csv"]
with (format = "txt"))
| extend report = parse_csv(report)
| extend Type = tostring(report[2])
| where Type == 'sha256'
| extend SHA256 = tostring(report[3])
| where SHA256 !in(SHA256_whitelist)
| extend Tag = tostring(report[4])
| extend Tweet = tostring(report[5])
| project SHA256, Tag, Tweet
);
union (
TweetFeed
| join (
DeviceProcessEvents
| where Timestamp > MaxAge
) on SHA256
), (
TweetFeed
| join (
DeviceFileEvents
| where Timestamp > MaxAge
) on SHA256
), (
TweetFeed
| join (
DeviceImageLoadEvents
| where Timestamp > MaxAge
) on SHA256
) | project Timestamp, DeviceName, FileName, FolderPath, SHA256, Tag, Tweet
2. Search IP addresses with monthly tweets feed
let MaxAge = ago(30d);
let IPaddress_whitelist = pack_array(
'XXX' // Some IP address you want to whitelist.
);
let TweetFeed = materialize (
(externaldata(report:string)
[@"https://raw.githubusercontent.com/0xDanielLopez/TweetFeed/master/month.csv"]
with (format = "txt"))
| extend report = parse_csv(report)
| extend Type = tostring(report[2])
| where Type == 'ip'
| extend RemoteIP = tostring(report[3])
| where RemoteIP !in(IPaddress_whitelist)
| where not(ipv4_is_private(RemoteIP))
| extend Tag = tostring(report[4])
| extend Tweet = tostring(report[5])
| project RemoteIP, Tag, Tweet
);
union (
TweetFeed
| join (
DeviceNetworkEvents
| where Timestamp > MaxAge
) on RemoteIP
) | project Timestamp, DeviceName, RemoteIP, Tag, Tweet
3. Search urls and domains with weekly tweets feed
let MaxAge = ago(30d);
let domain_whitelist = pack_array(
'XXX' // Some URL/Domain you want to whitelist.
);
let TweetFeed = materialize (
(externaldata(report:string)
[@"https://raw.githubusercontent.com/0xDanielLopez/TweetFeed/master/week.csv"]
with (format = "txt"))
| extend report = parse_csv(report)
| extend Type = tostring(report[2])
| where Type in('url','domain')
| extend RemoteUrl = tostring(report[3])
| where RemoteUrl !in(domain_whitelist)
| extend Tag = tostring(report[4])
| extend Tweet = tostring(report[5])
| project RemoteUrl, Tag, Tweet
);
union (
TweetFeed
| join (
DeviceNetworkEvents
| where Timestamp > MaxAge
) on RemoteUrl
) | project Timestamp, DeviceName, RemoteUrl, Tag, Tweet
👤 Author
📌 Disclaimer
Please note that all the data is collected from Twitter and sorted/served here as it is on best effort.
I have tried to tune as much as possible the searches trying to collect only valuable info. However please consider making your own analysis before taking any action related to these IOCs.
Anyway feel free to reach me out or to provide any kind of feedback regarding any contribution or suggestion.
By the community, for the community.