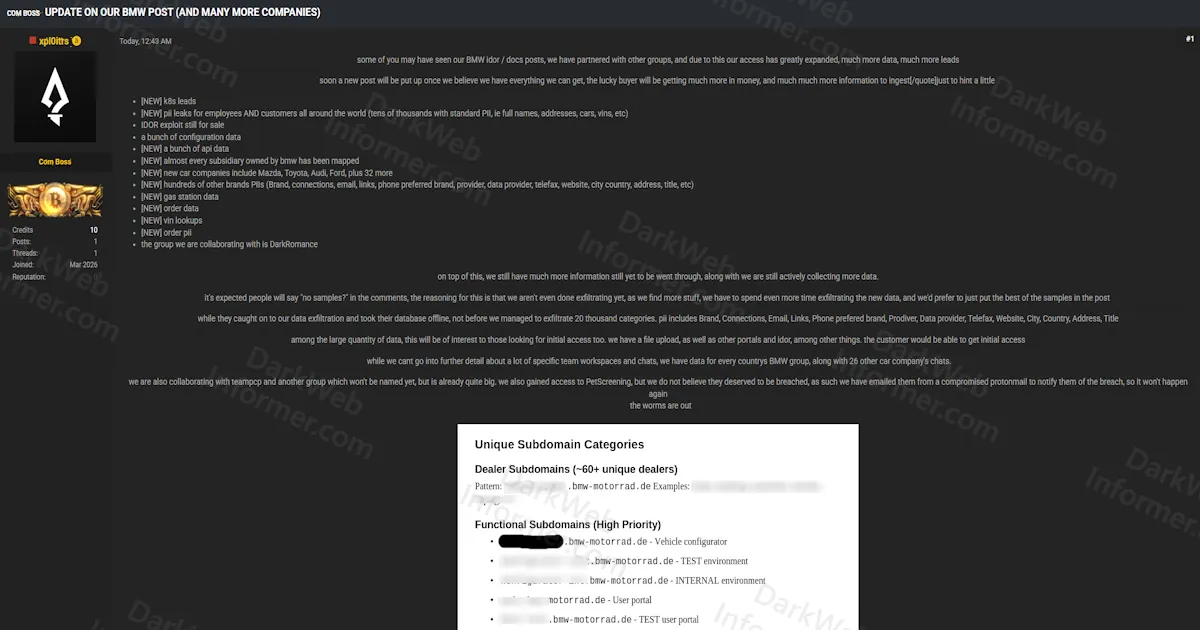
Threat Actors Claim Expanded BMW Breach With IDOR Exploit, Employee and Customer PII, and Data From Mazda, Toyota, Audi, Ford, and 32 Additional Automakers
Quick Facts
Incident Overview
A threat actor going by xpl0itts has posted an update claiming their previous BMW IDOR and document breach has expanded significantly. The actor states they have partnered with other groups, and their access now extends well beyond the original scope. They claim the exfiltration is still actively ongoing, and that a new comprehensive listing will be posted once they believe they have extracted everything available.
The update lists the following new data categories that have been added since the original breach:
- Kubernetes Leads: K8s infrastructure data from BMW's environment.
- Employee and Customer PII: Tens of thousands of records with full names, addresses, vehicle information, and VINs from customers worldwide.
- IDOR Exploit: The original Insecure Direct Object Reference vulnerability is still for sale.
- Configuration Data: Internal configuration files from BMW systems.
- API Data: Newly exfiltrated API-related data.
- Subsidiary Mapping: Nearly every subsidiary owned by BMW has been mapped.
- Additional Automakers: New car company data now includes Mazda, Toyota, Audi, Ford, and 32 additional manufacturers.
- Multi-Brand PII: Hundreds of other brands' PII including brand names, connections, email addresses, links, phone numbers, preferred brand data, provider information, telefax numbers, websites, city, country, address, and title fields.
- Gas Station Data: Newly acquired gas station records.
- Order Data and Order PII: Customer order records and associated personal information.
- VIN Lookups: Vehicle Identification Number lookup data.
The actor claims the target caught on and took their database offline, but not before the group managed to exfiltrate across 20,000 categories. They state they have data for every country's BMW group along with 26 other car companies' internal chats. The group also claims to have gained access to PetScreening but chose not to breach it, instead notifying them from a compromised ProtonMail account.
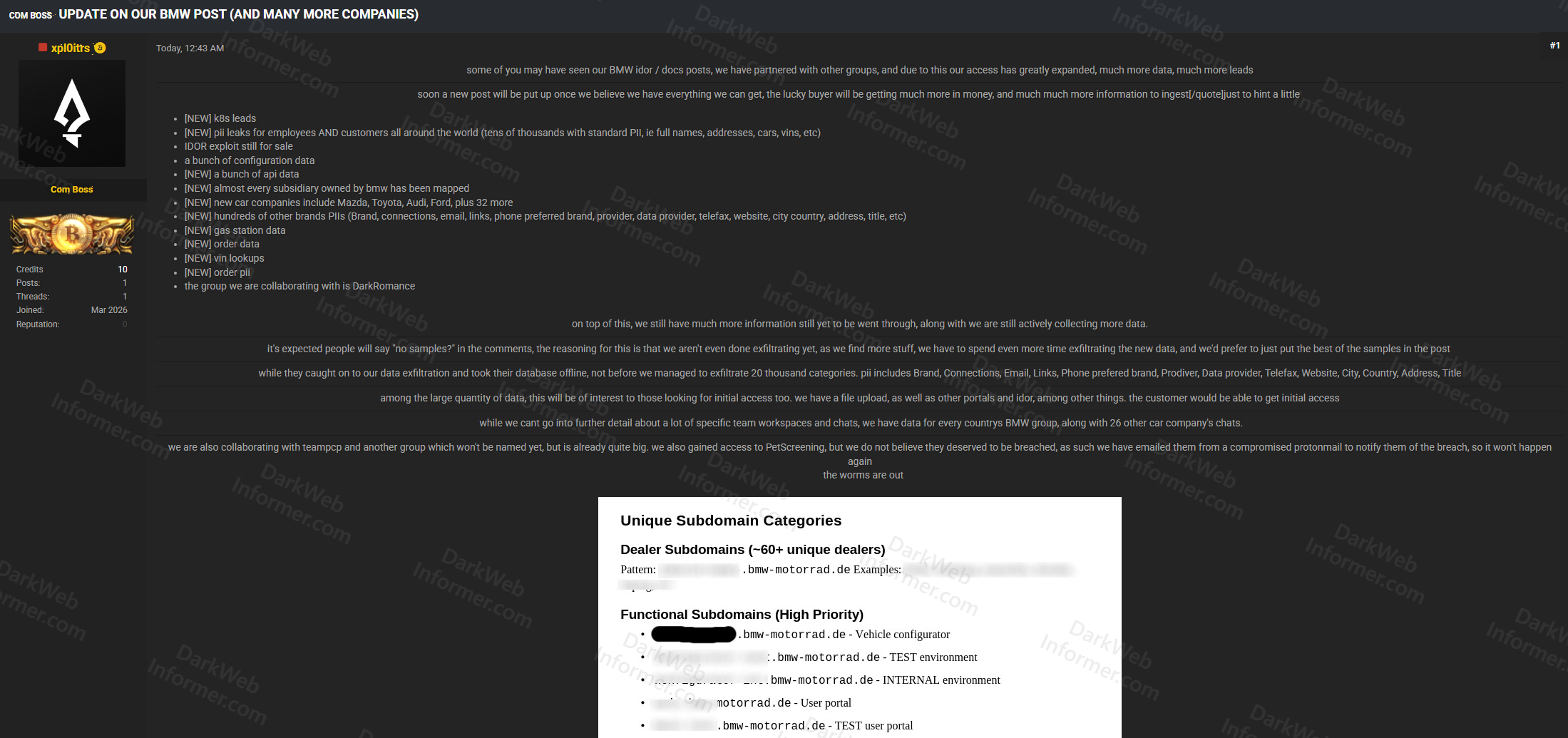
The post names three collaborating groups: DarkRomance, teamPCP, and one unnamed group described as "already quite big." The actor also mentions offering initial access via file upload and IDOR vulnerabilities across other portals. The listing explicitly states that no samples are provided yet because exfiltration is still in progress and they want to compile the best data before releasing samples publicly. The subdomain mapping screenshot shows approximately 60+ unique BMW Motorrad dealer subdomains along with functional subdomains including vehicle configurator, test environments, internal environments, and user portals.