Threat Actor Selling Root Access to South Korean Government Server With Lateral Movement to 42 Internal Hosts
Quick Facts
 South Korea
South Korea
Incident Overview
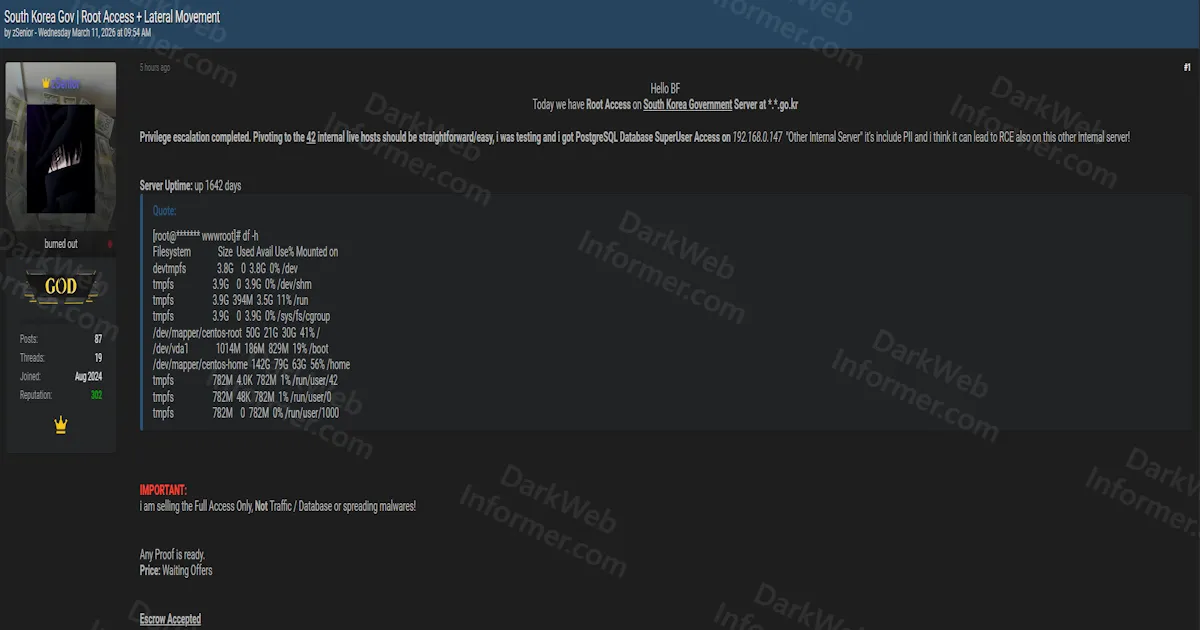
A threat actor operating under the handle zSenior is selling root-level access to a South Korean government server hosted on a *.go.kr domain, the official top-level domain reserved for South Korean government agencies. The actor claims to have completed full privilege escalation and states that pivoting to 42 internal live hosts from the compromised server should be straightforward.
Beyond the initial root access, the actor reports having obtained PostgreSQL database superuser access on a second internal server at 192.168.0.147, which they describe as containing PII. They also believe this secondary server may be vulnerable to remote code execution, further expanding the potential attack surface. The compromised server is running CentOS and has been online continuously for 1,642 days, with disk usage showing a 50GB root partition and a 142GB home partition at 55% capacity.
The actor emphasizes they are selling full access only and explicitly states this is not for traffic, database, or malware distribution. Proof is available upon request, pricing is open to offers, and escrow is accepted. This represents a significant national security concern given the government domain and the extensive lateral movement potential across dozens of internal systems.
Claim URL - For Subscribers Only
The claim URL for this listing can be found on the Threat Feed or Ransomware Feed for subscribers.