Sector Drainer Advertised as Crypto Wallet Drainer-as-a-Service With 0-Day Phantom Bypass, Hidden Drain, and Autowithdraw Capabilities
Quick Facts
Incident Overview
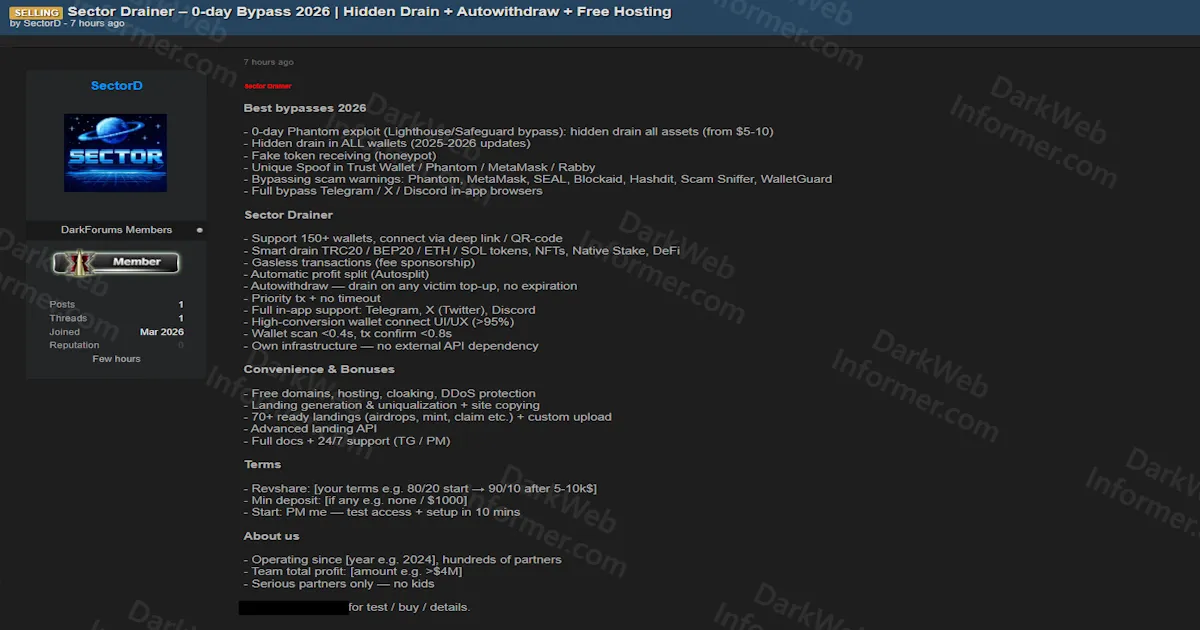
A threat actor going by SectorD is advertising a drainer-as-a-service platform called Sector Drainer, marketed as a full-stack crypto wallet draining solution with claimed 0-day exploits, scam warning bypasses, and turnkey phishing infrastructure. The actor claims the operation has been running since 2024 with hundreds of partners and over $4 million in total team profits.
The listing is broken into several capability categories:
- Exploit Capabilities: Claims a 0-day Phantom exploit that bypasses Lighthouse and Safeguard protections to perform hidden drains starting from assets as low as $5-10. The service also claims hidden drain functionality across all wallets updated through 2025-2026, fake token receiving via honeypot techniques, and unique spoofing for Trust Wallet, Phantom, MetaMask, and Rabby.
- Security Bypasses: Claims to bypass scam warnings on Phantom, MetaMask, SEAL, Blockaid, Hashdit, Scam Sniffer, and WalletGuard. Also claims full bypass of in-app browsers on Telegram, X (Twitter), and Discord.
- Drainer Features: Supports over 150 wallets with deep link and QR code connection methods. Capable of draining TRC20, BEP20, ETH, SOL tokens, NFTs, native staked assets, and DeFi positions. Includes gasless transactions via fee sponsorship, automatic profit splitting, and autowithdraw that triggers on any victim wallet top-up with no expiration. Claims wallet scan times under 0.4 seconds and transaction confirmation under 0.8 seconds on self-hosted infrastructure with no external API dependencies.
- Infrastructure: Includes free domains, hosting, cloaking, and DDoS protection. Provides 70+ pre-built landing pages for fake airdrops, mints, claims, and similar lures, along with a landing generation tool, site copying capabilities, and an advanced landing API.
- Business Model: Operates on a revshare basis starting at 80/20 (partner keeps 80%) scaling to 90/10 after reaching $5-10K in stolen funds. Minimum deposit varies, with some examples listing $1,000. Setup is claimed to take 10 minutes.
Worth noting that the actor's forum account was created in March 2026 with only 1 post, 1 thread, and 0 reputation, which is a common profile for newly registered accounts advertising DaaS platforms. The listing includes a high-conversion wallet connect UI/UX claim of over 95%, 24/7 support via Telegram, and full documentation. The actor directs interested parties to contact via Telegram or Session messaging.