Sage: Avast's Agent Detection & Response Layer That Guards AI Coding Agents Against Malicious Commands
A lightweight security layer from Gen Digital (Avast/Norton) that intercepts tool calls from Claude Code, Cursor, and OpenClaw — checking URLs against reputation APIs, scanning packages for supply-chain threats, and matching commands against YAML-based threat definitions. Think antivirus, but for AI agents.
Lightweight Agent Detection & Response (ADR) layer for AI agents — guards commands, files, and web requests
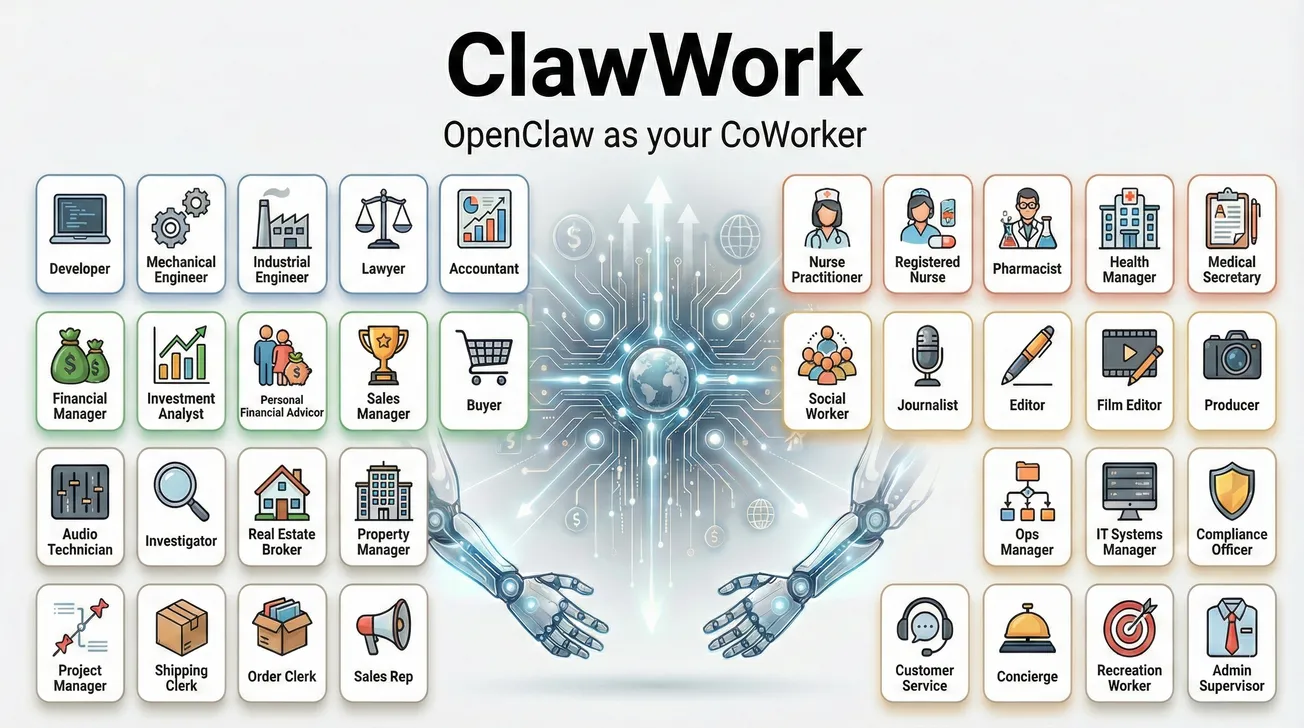
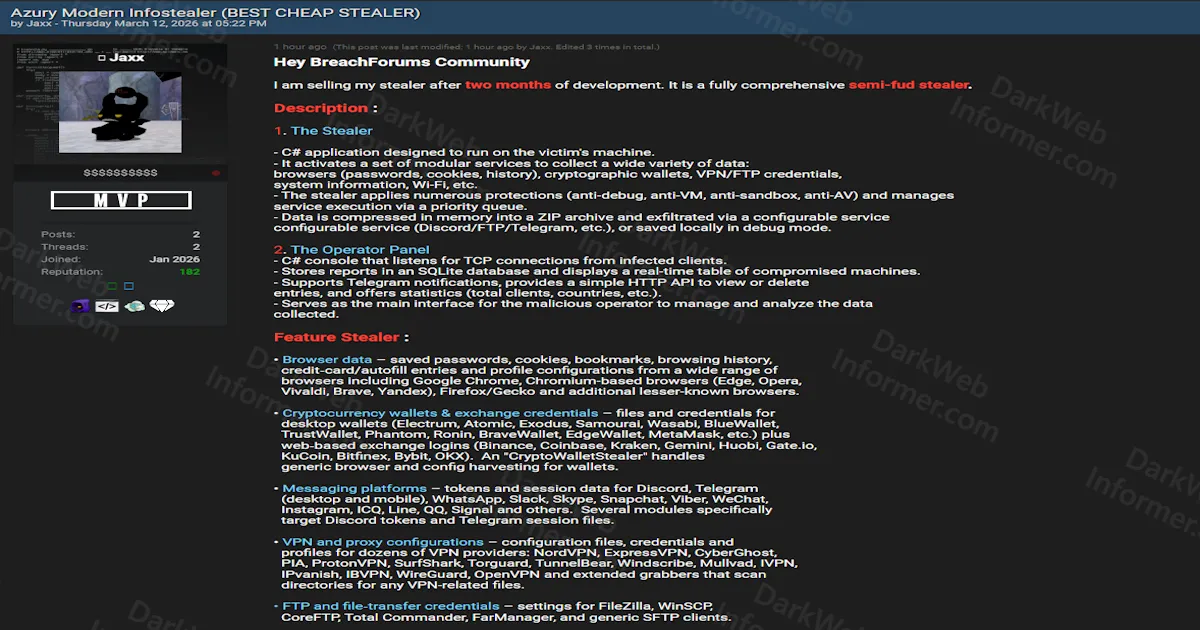
AI coding agents now run shell commands, write files, fetch URLs, and install packages on your behalf. Claude Code, Cursor, and OpenClaw all give agents broad access to your development environment. But what happens when a prompt injection tricks an agent into running curl against a malicious URL, or installing a typosquatted npm package, or writing a backdoor into your codebase? The agent follows instructions — it doesn't inherently know the difference between a legitimate command and a malicious one.
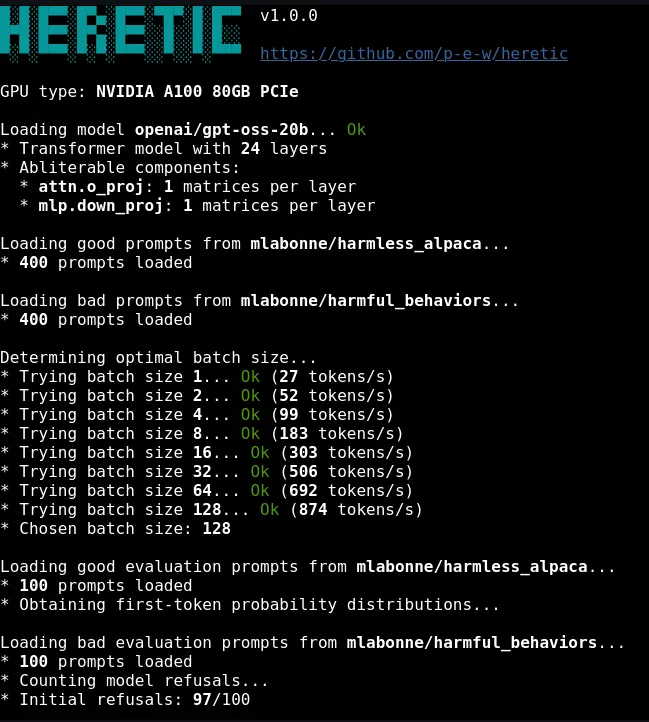
Sage is Gen Digital's (the parent company of Avast and Norton) answer to this problem. It's an Agent Detection & Response (ADR) layer that sits between the AI agent and the system, intercepting tool calls before they execute. It's a new category of security tooling — not protecting against AI threats, but protecting AI agents from being exploited as attack vectors.
// Detection Layers
// How It Works
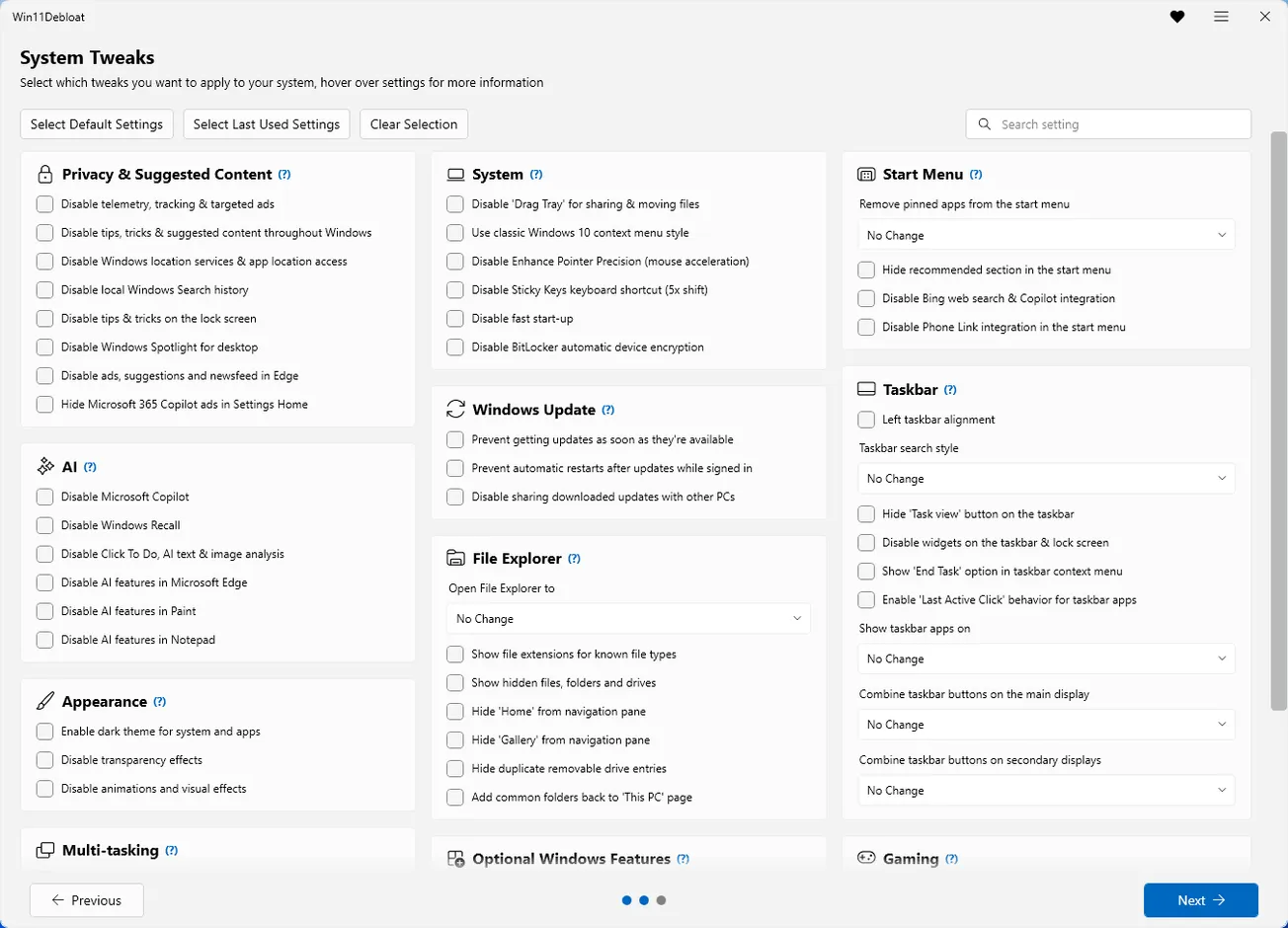
Sage hooks into the tool call pipeline of each supported platform. In Claude Code, it registers as a plugin that intercepts Bash commands, URL fetches, and file writes. In Cursor/VS Code, it runs as an extension. In OpenClaw, it installs as a plugin package. When a tool call comes through, Sage evaluates it against all four detection layers and returns a verdict: allow, warn, or block.
The threat definitions are YAML-based rules stored in the threats/ directory. These define patterns for dangerous operations — things like attempts to exfiltrate environment variables, write to sensitive system paths, download from known-bad domains, or install packages with suspicious naming patterns. The rules are versioned alongside the code and carry their own license (Detection Rule License 1.1).
// Platform Support
| Platform | Installation | Integration Method |
|---|---|---|
| Claude Code | Plugin marketplace | Plugin hook system |
| Cursor / VS Code | VSIX extension | Extension API + command palette |
| OpenClaw | npm package or source | Plugin system |
Claude Code installation is the simplest: two commands via the plugin marketplace. Cursor requires building the VSIX from source with pnpm and then enabling protection from the command palette. OpenClaw supports installation from npm directly or from source. All three platforms use the same core detection engine under the hood.
// Privacy Model
The privacy model is well-documented and transparent. The cloud components send hashes, not raw data, to Gen Digital's reputation infrastructure. For security-sensitive environments that can't tolerate any external communication, the cloud checks can be disabled entirely, falling back to local YAML-based threat definitions only. This is a reasonable trade-off — cloud reputation databases are significantly more comprehensive, but the local-only mode still provides meaningful protection.
// Who Built This
This comes from Gen Digital, the parent company of Avast, Norton, LifeLock, and AVG. That's significant context — this isn't a side project from a random developer. It's a security company with decades of experience in threat detection and reputation systems applying that expertise to a new attack surface: AI coding agents. The URL reputation and package reputation APIs that Sage calls into are backed by Gen Digital's existing threat intelligence infrastructure.
// Considerations
No MCP interception yet. The most significant current limitation. MCP (Model Context Protocol) tool calls (mcp__*) are not yet intercepted, meaning Sage can't guard against malicious operations routed through MCP servers. Given that MCP is becoming the standard integration layer for AI agents, this is a gap that needs closing.
Cloud dependency for full protection. The strongest detection layer (URL and package reputation) requires calling Gen Digital's cloud APIs. Fully offline operation is supported but offers reduced coverage. Organizations with strict data egress policies will need to evaluate whether hash-based lookups meet their requirements.
Platform coverage. Currently limited to Claude Code, Cursor/VS Code, and OpenClaw. Other popular agent frameworks (Windsurf, Aider, Continue, etc.) are not yet supported. The monorepo architecture with a shared core engine suggests adding new platforms should be relatively straightforward.
Threat rule licensing. The source code is Apache-2.0, but the threat detection rules in threats/ carry a separate "Detection Rule License 1.1." Users should review this license for any restrictions on use or redistribution of the threat definitions.
// Bottom Line
Sage represents a new and increasingly necessary category of security tooling. As AI coding agents gain deeper access to development environments — running shell commands, installing packages, writing files — the attack surface expands significantly. Prompt injection, typosquatted packages, and malicious URLs are real threats that agents are poorly equipped to defend against on their own.
Having a major security vendor like Gen Digital invest in this space adds credibility and brings real threat intelligence infrastructure to the problem. The four-layer detection approach (URL reputation, local heuristics, supply-chain checks, plugin scanning) covers the most important attack vectors, and the privacy model is transparent about what data leaves the machine. At 127 stars it's still early, but the backing, the architecture, and the problem it solves make Sage worth watching — and worth installing if you're running AI coding agents in any serious capacity.