India's Narcotics Control Bureau (NCB) has taken down a pan-India darknet drug distribution network operating under the name "Team Kalki," arresting two individuals and seizing narcotics valued at an estimated ₹5 crore (~$580,000 USD) on the international market.
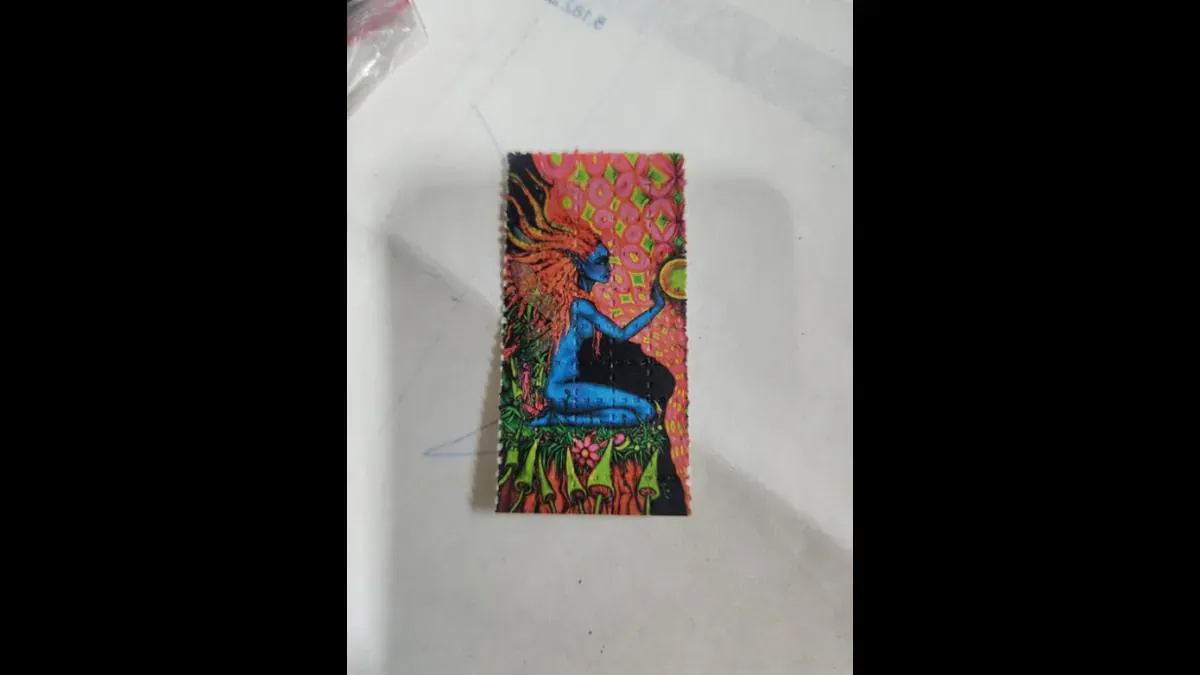
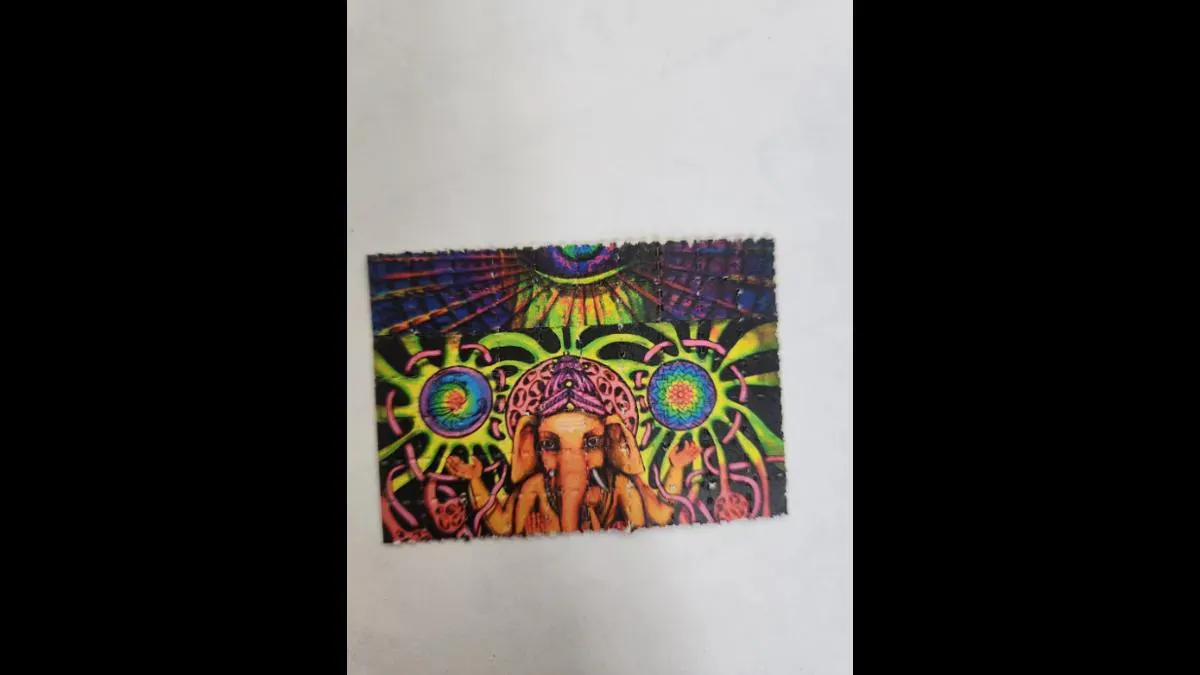
The operation, conducted in New Delhi following three months of intelligence gathering, resulted in the seizure of 2,338 LSD blotters, 160 MDMA (Ecstasy) pills (~77.5g), 73.6 grams of charas (cannabis resin), 3.6 grams of amphetamine, and 3.6 kilograms of liquid MDMA. The drugs were recovered from 13 domestically intercepted parcels and two international consignments originating from the Netherlands.
The Operators
The network was run by Anurag Thakur and his associate Vikas Rathi, both repeat offenders previously arrested under India's Narcotic Drugs and Psychotropic Substances (NDPS) Act. Rathi had served time in Tihar Jail for a charas trafficking case filed by the Delhi Police Special Cell, while Thakur was imprisoned for methamphetamine trafficking by the Delhi Police Crime Branch. The two met while incarcerated at Tihar and later built the Team Kalki operation together after their release.
Darknet Operations & OPSEC
Team Kalki initially established itself on the dark web forum Dread, where it maintained a four-star vendor rating, indicating a high volume of successful transactions. The operation later expanded to the encrypted messaging platform Session for order fulfillment and customer communication.
The network sourced LSD and MDMA from international darknet vendors based in the Netherlands, Poland, and Germany. Orders from buyers across India were received via Dread and Session, with fulfillment handled by packaging and dispatching parcels through India Post's Speed Post service and various private courier companies. Notably, a different courier office or booking account was used for each individual shipment as an anti-detection measure.
In certain areas of Delhi, the network employed a "dead drop" delivery method, placing drug parcels at pre-determined locations rather than handing them directly to buyers. Customers were then notified of the pickup location. This technique was reserved for repeat customers with a history of multiple prior orders.
The NCB suspects the network dispatched more than 1,000 parcels across India since January 2025. Some consignments were intercepted by law enforcement before delivery in Delhi, Tamil Nadu, Telangana, Kerala, and Karnataka.
Cryptocurrency Laundering
Payments were accepted exclusively in cryptocurrency, primarily Monero (XMR) and USDT (Tether), using unhosted wallets. For USDT transactions, temporary wallets were dynamically created for each payment, with funds immediately funneled through multiple layers of intermediary wallets to beneficiary wallets in an attempt to obscure the transaction trail.
Proceeds were routed through intermediary wallets with conversion fees of up to 10%, then converted to USDT and stored in cold wallets. In some cases, mule wallets with KYC-compliant accounts were used to funnel cryptocurrency proceeds into the formal banking system, a classic integration technique for laundering digital currency.
Multiple electronic devices and a cryptocurrency wallet linked to the operation were recovered during the arrests.
Broader Context
This operation is part of the NCB's sustained crackdown on darknet-enabled drug trafficking in India. Previous operations include Operation Ketamelon (2025), which dismantled India's only Level-4 darknet vendor "Ketamelon" operating out of Kerala, and Operation Zambada (2023), which targeted international darknet market supply chains.
The NCB says its investigation is ongoing, with efforts focused on identifying additional associates, tracing financial transactions, and uncovering the international supply chain connected to Team Kalki.
Dark Web Informer Note
You can follow the threads on Dread:
https://dreadytofatroptsdj6io7l3xptbet6onoyno2yv7jicoxknyazubrad[.]onion/d/DarknetMarketsIndia