GitHub: https://github.com/kn0x0x/CVE-2025-32756-POC
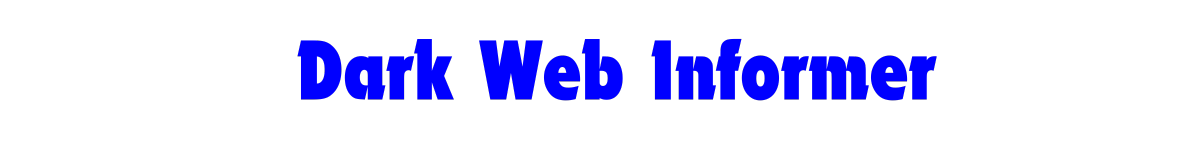
CVE-2025-32756: Fortinet RCE PoC
A proof-of-concept for the critical stack-based buffer overflow vulnerability (CVE-2025-32756) affecting Fortinet products.
Vulnerability
- CVSS: 9.8 (Critical)
- Type: Stack-based buffer overflow in AuthHash cookie processing
- Impact: Unauthenticated remote code execution
- Affected Products: FortiVoice, FortiMail, FortiNDR, FortiRecorder, FortiCamera
The vulnerability exists in the processing of the enc parameter in the /remote/hostcheck_validate endpoint, where improper bounds checking allows buffer overflow.
Usage
python3 fortinet_cve_2025_32756_poc.py target_ip [-p port] [-d]
Arguments:
target_ip: Target Fortinet device-p, --port: Target port (default: 443)-d, --debug: Enable debug output
Mitigation
Update to patched versions:
- FortiVoice: 7.2.1+, 7.0.7+, 6.4.11+
- FortiMail: 7.6.3+, 7.4.5+, 7.2.8+, 7.0.9+
- FortiNDR: 7.6.1+, 7.4.8+, 7.2.5+, 7.0.7+
- FortiRecorder: 7.2.4+, 7.0.6+, 6.4.6+
- FortiCamera: 2.1.4+
Disclaimer
For educational and research purposes only. Use only against systems you own or have permission to test.