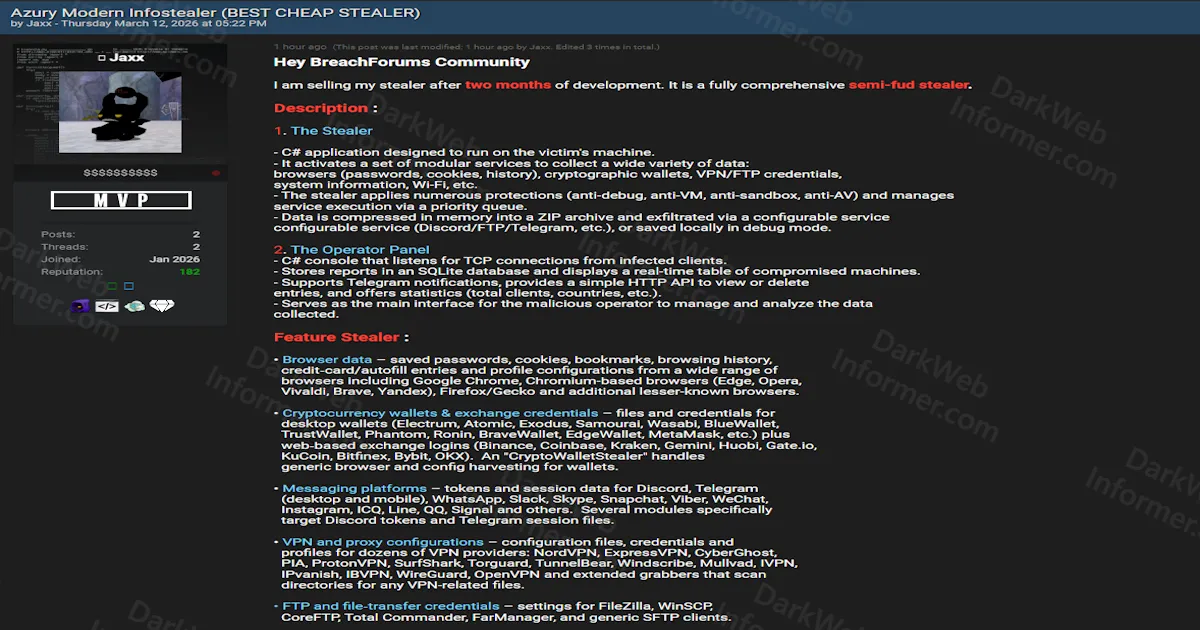
Azury Infostealer Source Code Sold for $100 With Full Operator Panel, Crypto Wallet Theft, and Keylogging Capabilities
Quick Facts
Incident Overview
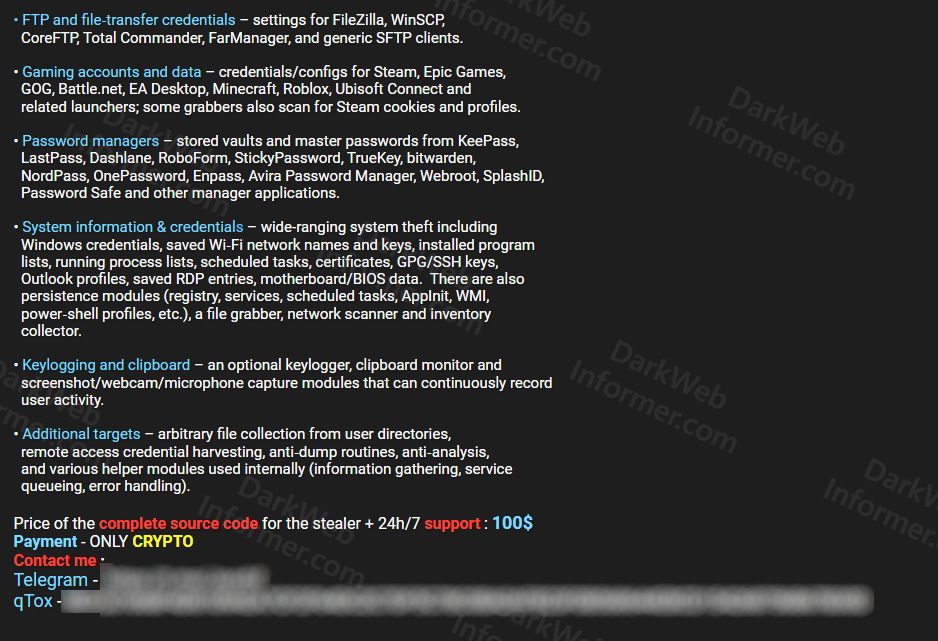
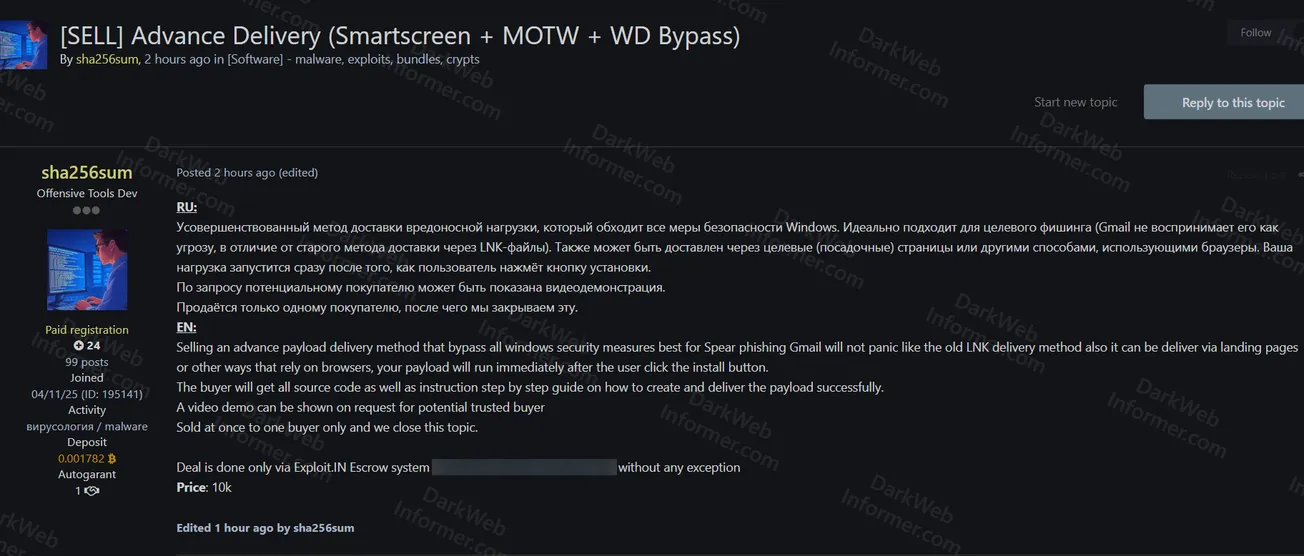
A threat actor going by Jaxx is selling the complete source code for a C# infostealer called Azury, described as a semi-FUD (fully undetectable) stealer built over two months of development. The package includes the stealer itself and a dedicated C# operator panel for managing infected machines, for $100.
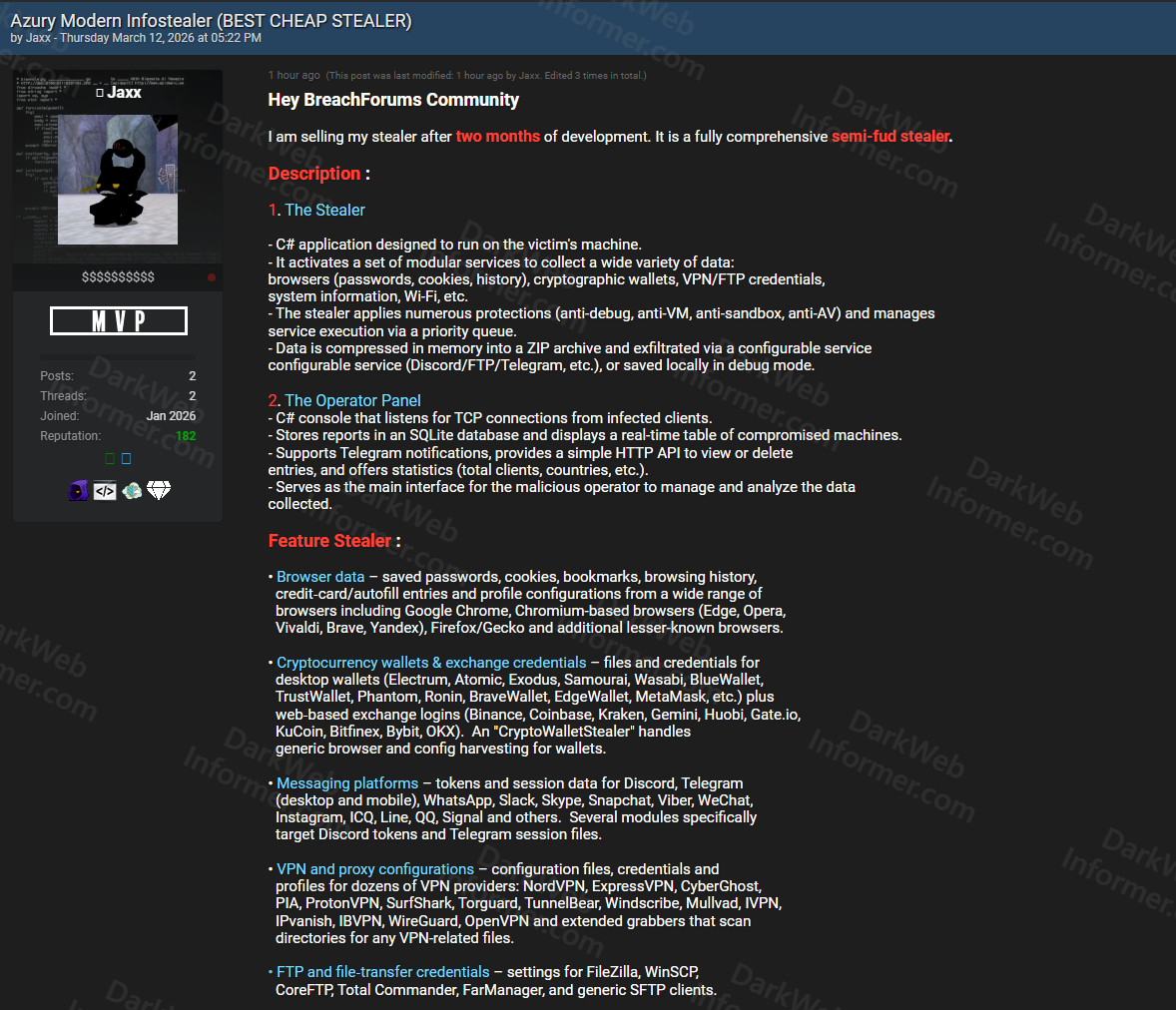
The stealer's feature set is extensive and covers nearly every category of sensitive data on a victim's machine. It targets browser data across Chrome, Edge, Opera, Vivaldi, Brave, Yandex, Firefox, and other Chromium and Gecko-based browsers, grabbing saved passwords, cookies, bookmarks, browsing history, credit card autofill entries, and profile configurations. Cryptocurrency wallets and exchange credentials are harvested from desktop wallets like Electrum, Atomic, Exodus, MetaMask, Phantom, and TrustWallet, as well as web-based exchange logins for Binance, Coinbase, Kraken, Gemini, KuCoin, Bybit, and others.
The stealer also grabs tokens and session data from messaging platforms including Discord, Telegram, WhatsApp, Slack, Skype, Snapchat, Signal, and more. VPN credentials are harvested from NordVPN, ExpressVPN, ProtonVPN, SurfShark, Mullvad, WireGuard, and over a dozen other providers. Password manager vaults from KeePass, LastPass, Dashlane, 1Password, Bitwarden, NordPass, and others are targeted, along with gaming accounts from Steam, Epic Games, Roblox, and Battle.net. Additional capabilities include keylogging, clipboard monitoring, webcam and microphone capture, arbitrary file collection, persistence mechanisms, and anti-analysis protections including anti-debug, anti-VM, and anti-sandbox measures. Data is exfiltrated as an in-memory ZIP archive via configurable channels like Discord, FTP, or Telegram.
Stealer Target Categories
Claim URL - For Subscribers Only
The claim URL and unredacted screenshots for this listing can be found on the Threat Feed or Ransomware Feed for subscribers.