📢 Unlock Exclusive Cyber Threat Intelligence
Powered by DarkWebInformer.com
Get foundational access to breach intelligence — track breaches, leaks, and threats in real-time with unfiltered screenshots and expert summaries.
⚠ Disclaimer
This report includes actual screenshots and/or text that may include unredacted personally identifiable information (PII) gathered from publicly available sources. The sensitive information presented within this report is intended solely for cybersecurity awareness and threat intelligence purposes. Dark Web Informer explicitly condemns unauthorized access, distribution, or misuse of the personal data displayed or referenced here. Users must treat exposed data responsibly and ethically.
📌 Overview
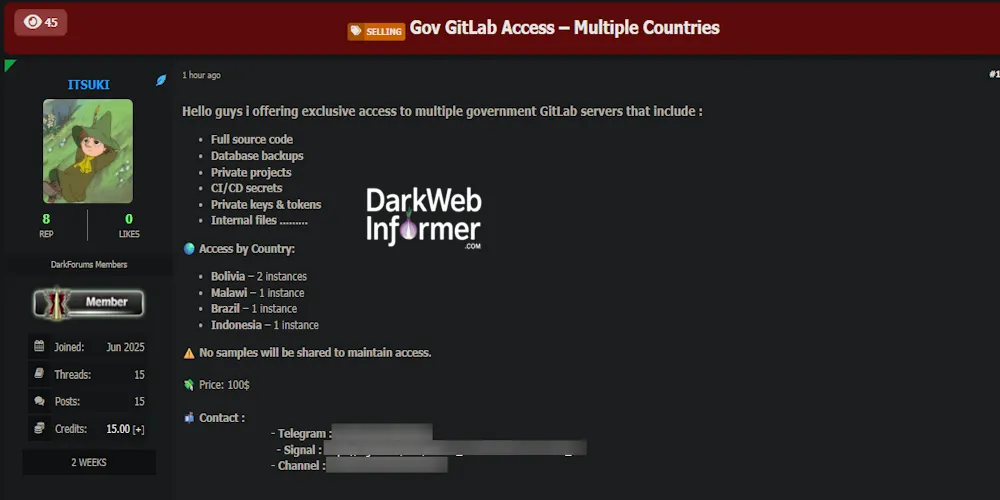
A threat actor using the alias ITSUKI has advertised access to multiple government GitLab servers spanning at least four countries, including Bolivia, Malawi, Brazil, and Indonesia. The listing was posted to DarkForums and claims each access point contains sensitive repositories, such as full source code, CI/CD secrets, private keys, internal documentation, and database backups. The actor emphasizes that no samples will be shared to maintain the integrity of the accesses being sold.
📊 Key Details
| Attribute | Information |
|---|---|
| Date | 2025-06-18, 11:34:23 AM |
| Threat Actor | ITSUKI |
| Victim Country | Bolivia (plus Malawi, Brazil, Indonesia) |
| Industry | Government Administration |
| Victim Organization | Not disclosed |
| Victim Site | Not disclosed |
| Category | Initial Access |
| Severity | High |
| Network | openweb |
Subscriber-only content…