Alleged Full Infrastructure Compromise of National Oil Ethiopia With 800GB ERP Database Exfiltration, Veeam and Kaspersky Compromise, and Ransomware Deployment
Quick Facts
Incident Overview
A threat actor going by ByteToBreach claims to have fully compromised the infrastructure of National Oil Ethiopia PLC (NOC), Ethiopia's state-owned oil company. This is not a simple database dump. The actor describes a complete infrastructure takeover that progressed through 8 distinct steps, culminating in ransomware deployment. The listing includes a detailed technical narrative of the intrusion, which is unusual for forum posts and suggests the actor wants to demonstrate credibility and operational sophistication.
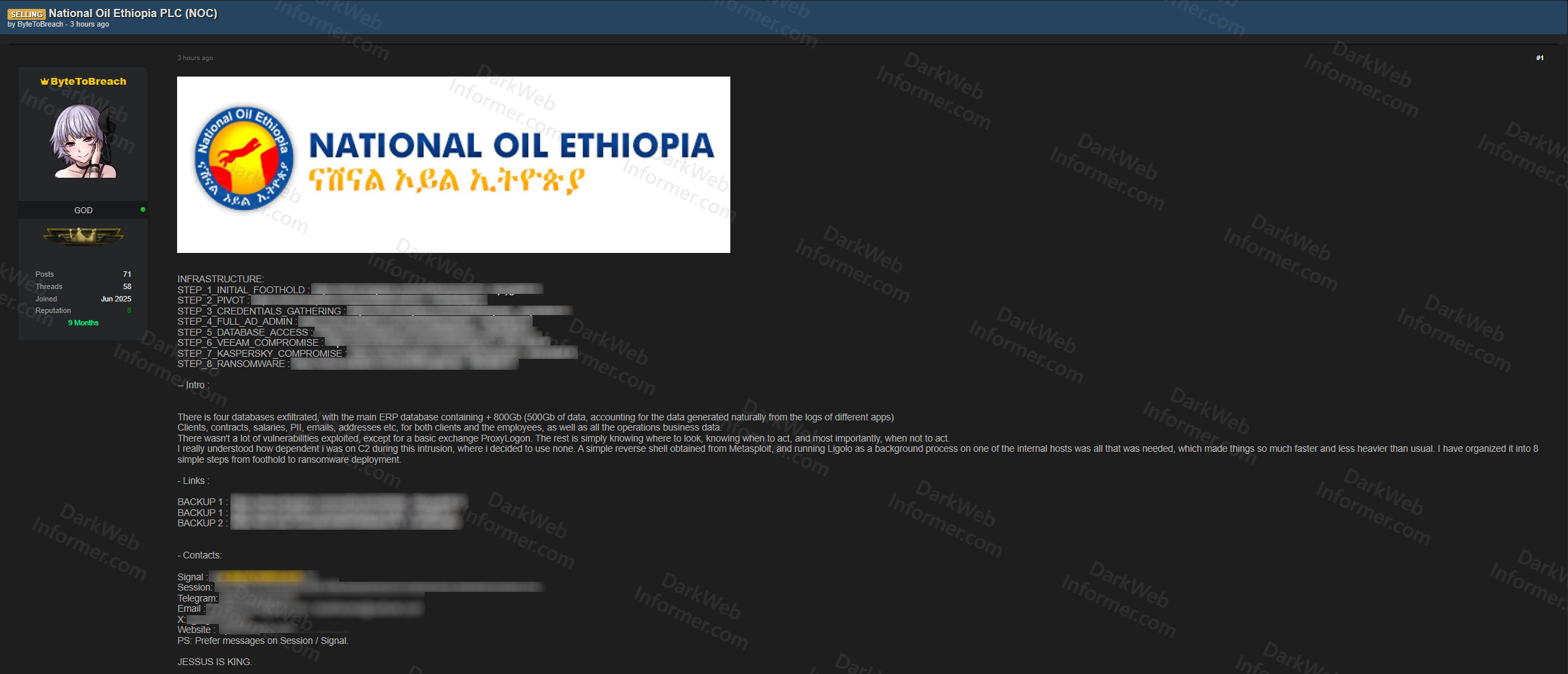
The actor outlines the following attack chain:
- Step 1: Initial Foothold: Gained entry through a basic Exchange ProxyLogon exploit. The actor notes there weren't many vulnerabilities to exploit beyond this entry point.
- Step 2: Pivot: Moved laterally from the compromised Exchange server into the internal network. The actor used a Metasploit reverse shell and ran Ligolo as a background process on an internal host for tunneling, noting this made things faster and lighter than relying on traditional C2 infrastructure.
- Step 3: Credential Gathering: Harvested credentials from internal systems.
- Step 4: Full AD Admin: Achieved full Active Directory administrator access, giving complete control over the domain environment.
- Step 5: Database Access: Accessed and exfiltrated four databases totaling over 800GB of data. The main ERP database alone contained 500GB, with the remaining data generated from application logs.
- Step 6: Veeam Compromise: Compromised the Veeam backup infrastructure, likely to destroy or encrypt backups and prevent recovery.
- Step 7: Kaspersky Compromise: Compromised the Kaspersky security solution, disabling or bypassing endpoint protection across the environment.
- Step 8: Ransomware: Deployed ransomware across the infrastructure.
The exfiltrated data allegedly includes client records, contracts, salaries, PII, email addresses, physical addresses, and all operational business data for both clients and employees. The actor emphasizes that the intrusion relied more on knowing where to look and when to act than on exploiting numerous vulnerabilities. Backup links and contact information via Signal, Session, Telegram, email, X, and a website are provided. The actor prefers communication via Session or Signal.