Alleged Breach of Alyna Exposes 18,000 Users With Passwords, GPS Coordinates, and Booking Data From Kuwaiti Laundry and Cleaning App
Quick Facts
Incident Overview
A threat actor going by Sorb claims to be selling the full user database from Alyna, a Kuwait-based mobile app that provides laundry and cleaning services. The company was founded in 2019 in Hawally, Kuwait, and operates as an unfunded app-based platform available on both Google Play and the Apple App Store.
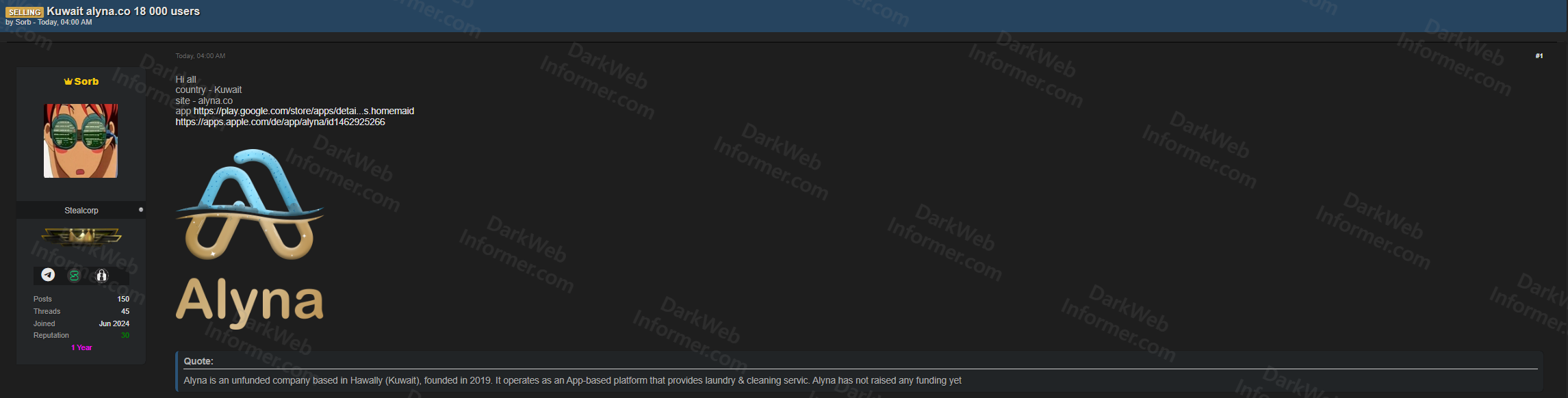
The database contains 18,000 total user records with the following data points:
- Account Data: User IDs, account types, names (including Arabic names), gender, date of birth, email addresses, mobile numbers, profile images, registration dates, and email verification status.
- Credentials: Passwords hashed with MD5, which is a weak and easily crackable hashing algorithm. The actor also mentions a combo list of email/phone hash pairs (13,500 mail hashes and 17,000 phone hashes).
- Location Data: GPS coordinates (latitude and longitude), booking addresses, street addresses, and area information. This is particularly sensitive as it reveals where users live or regularly request services.
- Device and Platform Data: Operating system type, device language, push registration IDs, and social media registration source.
- Service Data: Preferred services, house type IDs, room counts, booking details, likes, guest status, and anonymization flags.
- Tokens: Kfast tokens that may allow session hijacking or unauthorized account access.
The listing is priced at $300 with escrow available, and the actor specifies this is a single-buyer exclusive sale ("sales in one hands"). The deduplicated counts show 13,500 unique emails and 16,000 unique phone numbers. Given the nature of the service, the GPS and booking address data effectively maps where users live across Kuwait, making this a physical safety concern beyond typical PII exposure.